Unified Scoping
Guide (USG)
A zone-based model to apply a data-centric security approach for scoping sensitive & regulated data — covering CUI, CMMC, PCI DSS, PHI, PD, IP and more. The official scoping guidance for the SCF Conformity Assessment Program.
The Unified Scoping Guide — Free CMMC & Sensitive Data Scoping.
No registration — no cost — no restrictions. Version 2026.1 now available.
Everything You Need to
Scope Sensitive Data — Free
The Unified Scoping Guide is published as a comprehensive, fully-documented reference — not a summary or teaser. The full guide covers all 9 zones in detail, six real-world scoping scenarios, data flow diagram guidance, Zero Trust scoping, CMMC asset category mappings, appendices on VDI scoping, control applicability, and more.
No registration. No cost. No restrictions. Download, share and use freely.
⇓ Download the Unified Scoping Guide (PDF)Define Your Assessment Boundary
with the USG Zone Model
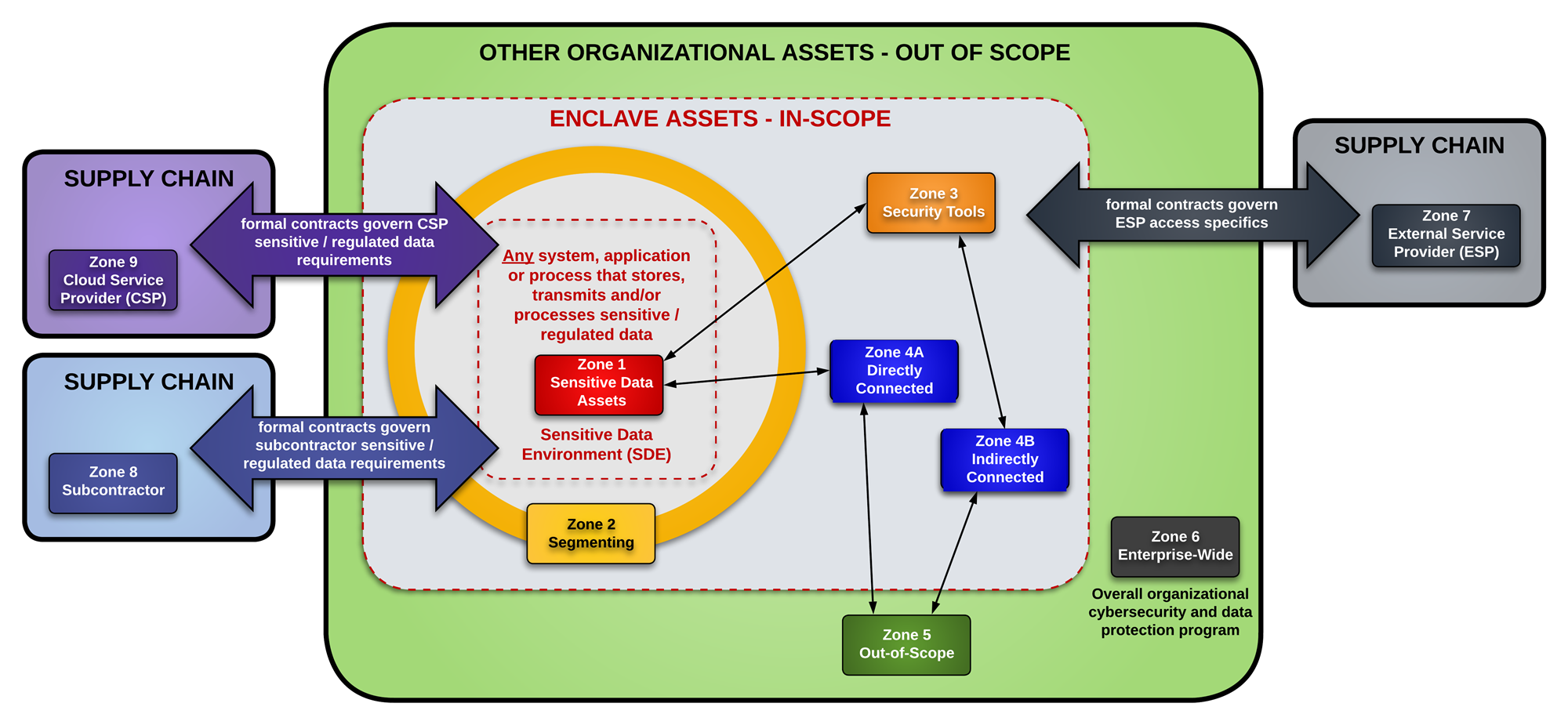
The USG uses nine distinct zones to categorize every asset in your environment based on one fundamental question: how does this system relate to sensitive or regulated data?
At the center is the Sensitive Data Environment (SDE) — the systems that directly Process, Store or Transmit (P/S/T) sensitive data. Every other asset is then classified by its proximity and connectivity to that core.
This model makes it immediately clear which systems require controls, which provide security functions, which are connected in scope, and which are genuinely out of scope. The result is a defensible, auditor-ready assessment boundary — without over-scoping your entire network.
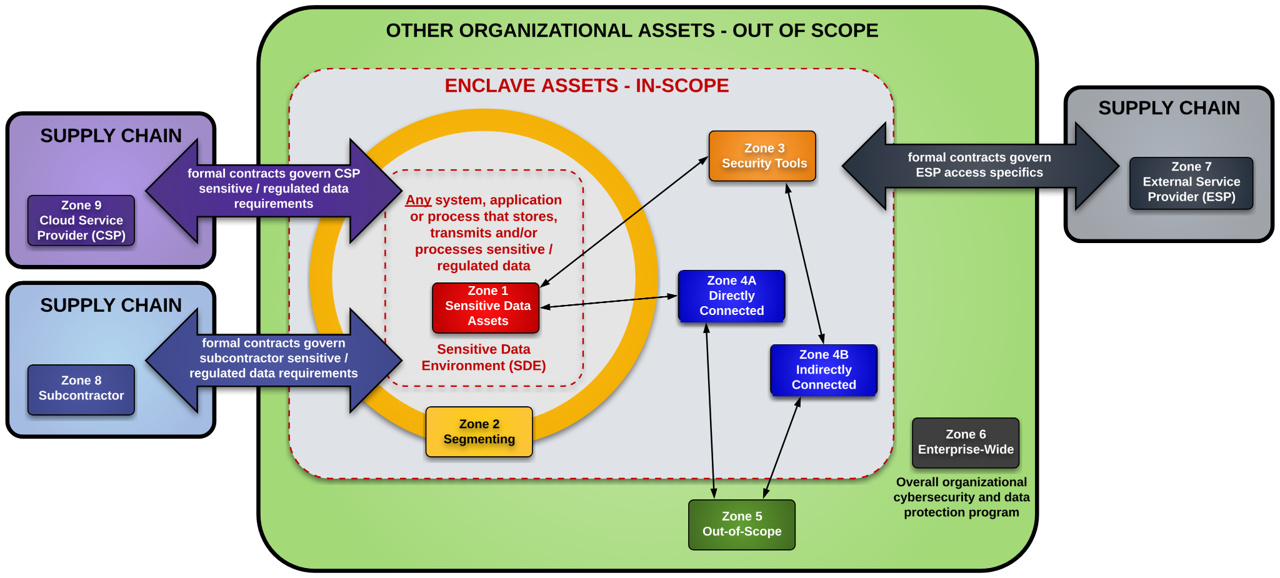
The Unified Scoping Guide Zone Map
This diagram illustrates how all 9 zones relate to each other and to the Sensitive Data Environment (SDE) — showing connectivity, segmentation, and scope boundaries at a glance.
The Data-Centric Approach
to Sensitive Data Scoping
In practical terms, cybersecurity and data protection controls exist to protect an organization’s data. Assets such as laptops, servers and network infrastructure are commodities that can be replaced — but the data residing on those devices cannot. This concept of being data-centric is crucial when establishing the scope for control applicability.
The Unified Scoping Guide (USG) is the definitive free CMMC scoping guide and sensitive data scoping framework, helping organizations define the scope of regulated data where it is Processed, Stored and/or Transmitted (P/S/T). It categorizes system components based on three key factors:
The USG extends the landmark PCI DSS Scoping Model and Approach — the most mature, internationally recognized scoping framework — applying that methodology to all types of sensitive and regulated data, far beyond payment cards.
Scoping ≠ Applicability. Being in scope does not mean every control applies everywhere. A network firewall cannot complete user awareness training; a person cannot have a patch applied. The USG resolves this common misconception that makes compliance cost-prohibitive.
Fiduciary Warning
Failure to perform adequate scoping due diligence may result in every system, application and service being considered in scope — making compliance cost-prohibitive or technically impossible. Scoping should be treated as a fiduciary responsibility.
P/S/T Defined
Store — data at rest (media, memory, paper). Process — data actively in use (accessed, edited, viewed). Transmit — data being transferred between assets (digital or physical).
The 9 Zones of the Unified
Scoping Guide Explained
The USG uses nine zones to categorize every system component based on its interaction with sensitive and regulated data. This model makes clear which systems require controls — and provides a defensible, documented rationale for every scoping decision.
Sensitive Data Assets
All systems, applications and services that Process, Store and/or Transmit sensitive/regulated data. These are the core assets of the Sensitive Data Environment (SDE) — the primary target of every control.
Segmenting
Network devices or hypervisors that provide segmentation — firewalls, ACL-enforcing devices and ZTA micro-segmentation components. They prevent sensitive data contamination from spreading to uncontrolled environments. Assessors will verify effectiveness.
Security Tools
Systems providing security-related or IT-enabling services that affect SDE security — Active Directory, DNS, NTP, patch management, SIEM, antimalware, MFA, VPN, IDS/IPS, DLP, FIM and vulnerability management platforms.
Connected
Any system capable of communicating with the SDE. If it can potentially impact the security of sensitive data, it is in scope. Divided into two sub-categories: Directly Connected (4A) and Indirectly Connected (4B).
Directly Connected
Systems outside the SDE capable of communicating directly with a Zone 1 asset. Any system outside the SDE with a direct logical path to a system that P/S/Ts sensitive data is a 4A device.
Indirectly Connected
Systems without direct SDE access that can reach Connected or Segmenting systems — such as an admin workstation managing a firewall, or an upstream patching system feeding into connected infrastructure.
Out-of-Scope
Assets completely isolated from the SDE. Must satisfy four tests: does not P/S/T sensitive data; not on the same network segment; cannot connect to the SDE; and cannot impact any in-scope security control.
Enterprise Wide
Enterprise-wide security controls beyond the SDE boundary — corporate security policies, standards and procedures affecting the entire organization’s cyber and physical security posture across all segments.
External Service Providers
Third-party organizations providing services, technologies, facilities and/or people — consulting, HR/payroll, MSPs, MSSPs, document destruction. Formal contracts and “flow-down” requirements must be assessed for each ESP.
Subcontractors
Third-parties necessary to execute the in-scope contract who may create, access, receive, store or transmit sensitive/regulated data as part of contract performance. Distinct from general ESPs by contractual involvement.
Cloud Service Providers (CSP)
ESPs providing cloud computing services — SaaS, PaaS and IaaS — with five essential characteristics: on-demand self-service, broad network access, resource pooling, rapid elasticity and measured service. Four deployment models: private, community, public and hybrid cloud. CSPs processing CUI must generally meet the FedRAMP Moderate baseline per DFARS 252.204-7012.
CMMC Asset Categorization
Decision Tree
Use this logic diagram to walk through the correct zone assignment for any asset in your environment — systematically and defensibly.
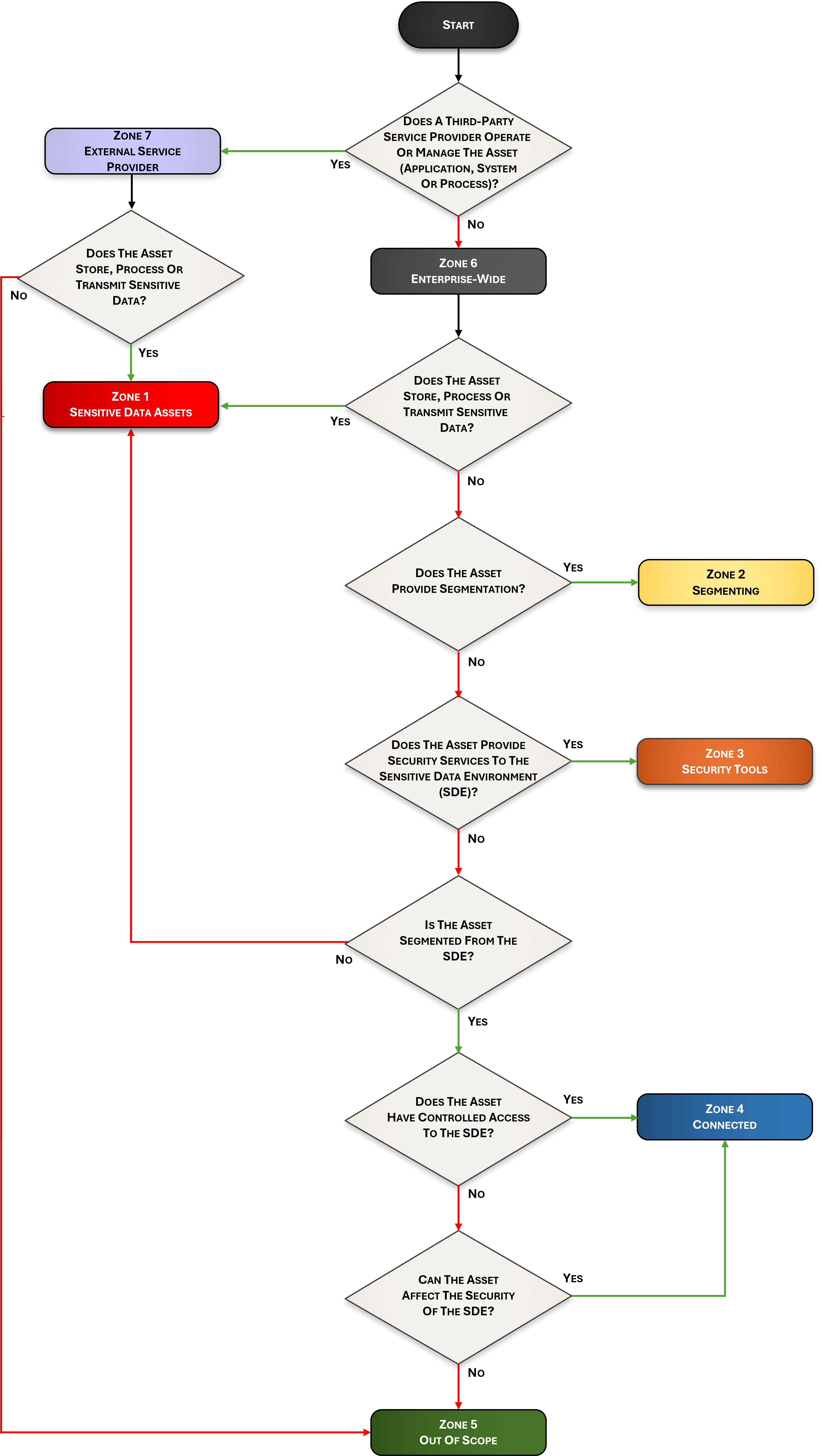
Every asset in your environment — servers, workstations, cloud instances, network devices, third-party services — needs to be classified into a USG zone. This decision tree walks you and your assessor through the logic steps in sequence, producing a documented, repeatable rationale for every categorization decision.
Work through the steps below to determine where any asset belongs:
Does it Process, Store or Transmit sensitive data?
If yes, the asset is a core component of the Sensitive Data Environment.
→ Zone 1: Sensitive Data AssetDoes it provide network segmentation?
Firewalls, routers, hypervisors and ZTA micro-segmentation components that control traffic between zones.
→ Zone 2: SegmentingDoes it provide security tooling that affects the SDE?
Identity, patching, logging, antimalware, MFA, SIEM, DLP — systems whose compromise could impact SDE security.
→ Zone 3: Security ToolsDoes it connect directly or indirectly to in-scope systems?
Direct logical path to a Zone 1 asset = 4A. Can reach Zone 2/3 systems (e.g., an admin workstation managing a firewall) = 4B.
→ Zone 4A or 4B: ConnectedIs it completely isolated — no SDE connectivity whatsoever?
Must satisfy all four out-of-scope tests: no P/S/T, no shared segment, no connection path, no ability to impact SDE controls.
→ Zone 5: Out-of-ScopePeople, Processes, Technologies,
Data & Facilities (PPTDF)
The PPTDF model provides a comprehensive lens for viewing control applicability within the assessment boundary. Controls must be correctly mapped to each component — not applied uniformly to everything in scope.
People
Controls applying to humans — training, background checks, NDAs and acceptable use. A device cannot complete user awareness training.
Processes
Administrative work — policies, standards, procedures, incident response plans, governance and workflow management.
Technologies
Systems, applications and services — secure baselines, patching, antimalware and technical controls. A person cannot be patched.
Data
Data protection controls — encryption at rest and in transit, data classification, metatags, DLP and data lifecycle management.
Facilities
Physical infrastructure — access controls, HVAC, visitor management, surveillance, proximity badges and environmental controls.
CUI, PHI, PCI DSS & All 10
Sensitive Data Types Covered
The USG applies to any organization handling sensitive or regulated data. All ten data types below are expressly addressed by the zone-based scoping guidance.
Controlled Unclassified Information
US Government data governed by Executive Order 13556 and NIST SP 800-171. Required for DoD contractors under DFARS 252.204-7012 and the CMMC program. The USG includes a complete CMMC scoping section.
Federal Contract Information
Broad category under FAR 52.204-21. Information not intended for public release, generated under a government contract. Forms the basis of CMMC Level 1 — 15 core cybersecurity requirements.
Personal Data / PII
Information that can distinguish or trace an individual’s identity. Governed by OMB M-07-16, GDPR, CCPA and sector-specific laws. Context determines whether PD rises to the level of sensitive data.
Protected Health Information
Individually identifiable health information under HIPAA. Applies to covered entities and business associates. Requires strict access controls, encryption and breach notification compliance.
Cardholder Data
Payment card data governed by PCI DSS — the most mature scoping model globally, whose concepts form the foundation of the USG. Proper segmentation can dramatically reduce PCI DSS scope and compliance cost.
Intellectual Property
Trade secrets, patents, product designs and confidential competitive data. Often unregulated by statute yet critically sensitive — loss can be catastrophic for competitive advantage and business valuation.
Attorney-Client Privilege Information
Confidential attorney-client communications protected by legal privilege. Inadvertent disclosure can permanently waive privilege protections, making strict data handling controls essential.
Student Educational Records
Student records under the Family Educational Rights and Privacy Act. Applicable to educational institutions receiving federal funding, governing access to and disclosure of student information.
Export-Controlled Data
Defense articles and technical data under ITAR; dual-use items under EAR. Critical for defense contractors and technology exporters subject to State and Commerce Department jurisdiction.
Critical Infrastructure Information
Information about the nation’s critical sectors — energy, water, transportation, finance and communications — requiring heightened protection against unauthorized disclosure or adversarial exploitation.
Segmentation & the
Assessment Boundary
Without adequate network segmentation (a flat network), the entire network is expected to be in scope for an assessment. Network segmentation is a highly beneficial process to isolate systems that P/S/T sensitive data from those that do not — potentially reducing scope and compliance cost dramatically.
The USG eliminates ambiguity by defining two precise segmentation terms for enclave scoping:
Isolation — No Logical Access
Network traffic between two or more assets is not permitted whatsoever. This is the standard required for Zone 5 (Out-of-Scope) assets to be confirmed as truly out of scope.
Controlled Access — Restricted Logical Access
Access between assets is permitted but restricted to defined parameters — specific ports, protocols, services and connection directions. Achieved through firewalls, routers, hypervisors and ZTA micro-segmentation. More common than isolation.
The assessment boundary defines the “security perimeter” — encompassing not just the SDE, but all PPTDF that influence SDE security and therefore require applicable security controls.
It may be a simple SDE enclave or a complex arrangement of on-premises, cloud-based and third-party components. The zone-based approach handles both.
Official CMMC Scoping Guidance:
The USG & SCF CAP
The Secure Controls Framework (SCF) has designated the Unified Scoping Guide as the official scoping guidance for the SCF Conformity Assessment Program (SCF CAP).
The SCF CAP is designed to conduct Third Party Assessment, Attestation and Certification Services (3PAAC Services). Clear and defensible scoping guidance is a necessity for designating cybersecurity and data protection controls as in or out of scope for any formal assessment or certification effort.
By adopting the USG as its scoping standard, the SCF CAP ensures that assessment boundaries are established using a transparent, methodology-driven approach — reducing ambiguity between organizations and their assessors, and producing results that withstand regulatory scrutiny.
“The Secure Controls Framework (SCF) designated the USG as the official scoping guidance for the SCF’s Conformity Assessment Program (SCF CAP), designed to conduct Third Party Assessment, Attestation and Certification Services (3PAAC Services).”
Defined Assessment Boundaries
The USG provides a structured method so assessors and organizations share a common, documented scoping language with a defensible rationale.
Third-Party Assessment Support
The USG supports 3PA processes by giving assessors a clear, documented framework for scoping decisions that can be communicated to regulators.
CMMC & DoD Alignment
Dedicated guidance on 32 CFR Part 170 / CMMC: CUI Assets, SPAs, CRMAs, Specialized Assets and Out-of-Scope Assets, with a comparison matrix to USG zones.
Cloud & ESP Coverage
Zones 7, 8 and 9 provide explicit scoping guidance for External Service Providers, Subcontractors and Cloud Service Providers across all deployment and service models.
Zero Trust Scoping
Dedicated ZTA scoping section covers DoD Zero Trust Overlays, DHS CISA ZTCF technology categorizations, and why ZTA does not eliminate scoping obligations.
The USG Ecosystem
The Unified Scoping Guide is part of a broader open-source ecosystem of cybersecurity and data protection guidance. The USG is developed and maintained in collaboration with ComplianceForge and the Secure Controls Framework (SCF).
ComplianceForge publishes the full USG on its free guides page, making this resource accessible to all organizations regardless of size or budget. The USG complements the Secure Controls Framework and the Digital Security Program (DSP) documentation toolkit — giving organizations a complete, integrated approach to cybersecurity compliance.
Access the current USG page on ComplianceForge alongside other free cybersecurity resources:
Frequently Asked Questions
About Sensitive Data Scoping
What is the Unified Scoping Guide (USG)?
The USG is a free, open-source zone-based model for scoping sensitive and regulated data environments. It applies a data-centric security approach to classify all system components into 9 zones based on their interaction with sensitive data — covering CUI, CMMC, PCI DSS, PHI, PD, IP, FERPA, ITAR/EAR, ACPI and CII.
Is the USG free to use and download?
Yes. The Unified Scoping Guide is completely free and publicly available. Download the PDF here — no registration, no cost, no restrictions on use.
Who should use the Unified Scoping Guide?
Any organization handling sensitive or regulated data — defense contractors (CMMC/CUI), healthcare organizations (HIPAA/PHI), financial services (PCI DSS), educational institutions (FERPA), government contractors (FCI/CUI), businesses with IP or export-controlled data, and their assessors and auditors.
Is the USG a CMMC scoping guide?
The USG includes a dedicated CMMC section covering 32 CFR Part 170 scoping criteria and all five CMMC asset categories — CUI Assets, Security Protection Assets (SPA), Contractor Risk Managed Assets (CRMA), Specialized Assets (SA) and Out-of-Scope Assets (OOSA) — with a comparison matrix to USG zones.
Does the USG cover PCI DSS scoping?
The USG was built upon PCI DSS scoping concepts — the most mature and internationally recognized model for sensitive data scoping. Without proper segmentation, an entire network may be in scope for PCI DSS. The USG extends that philosophy to all types of sensitive data.
Does Zero Trust Architecture eliminate scoping requirements?
No. The USG is explicit: ZTA is not a “magic bullet” to eliminate scoping requirements. ZTA micro-segmentation components are Zone 2 (Segmenting) assets and remain in scope. The USG includes dedicated ZTA scoping guidance covering DoD overlays and DHS CISA’s ZTCF.
What CMMC scoping scenarios does the USG include?
Six detailed network scoping scenarios: CUI on a flat network; CUI on a segmented on-premises network; CUI on a virtual/cloud network; CUI on a hybrid network; Sensitive IP & PD on a flat network; and Sensitive IP & PD on a segmented network — each with complete scoping exercises.
What is the difference between scoping and control applicability?
Scoping determines which PPTDF are within the assessment boundary. Applicability determines which specific controls apply to each in-scope component. A network firewall cannot complete user training; a person cannot have a configuration baseline applied. The USG addresses both clearly.
Does the USG serve as a CMMC Level 1 and Level 2 scoping guide?
Yes. The USG provides dedicated scoping guidance for all three CMMC levels. For CMMC Level 1 (FCI assets under FAR 52.204-21), Level 2 (CUI assets under 32 CFR Part 170 / NIST SP 800-171), and Level 3. The guide maps all five CMMC asset categories — CUI Assets, Security Protection Assets (SPA), Contractor Risk Managed Assets (CRMA), Specialized Assets (SA) and Out-of-Scope Assets (OOSA) — directly to the USG zone model.
Download the Free CMMC & Sensitive Data Scoping Guide
The Unified Scoping Guide is free and open to all organizations. Download the full guide, explore real-world scoping scenarios for CUI, PCI DSS, PHI and more — and apply a consistent, defensible zone-based methodology to your sensitive data environment.